Behavioral Security for Cloud Network and Identity
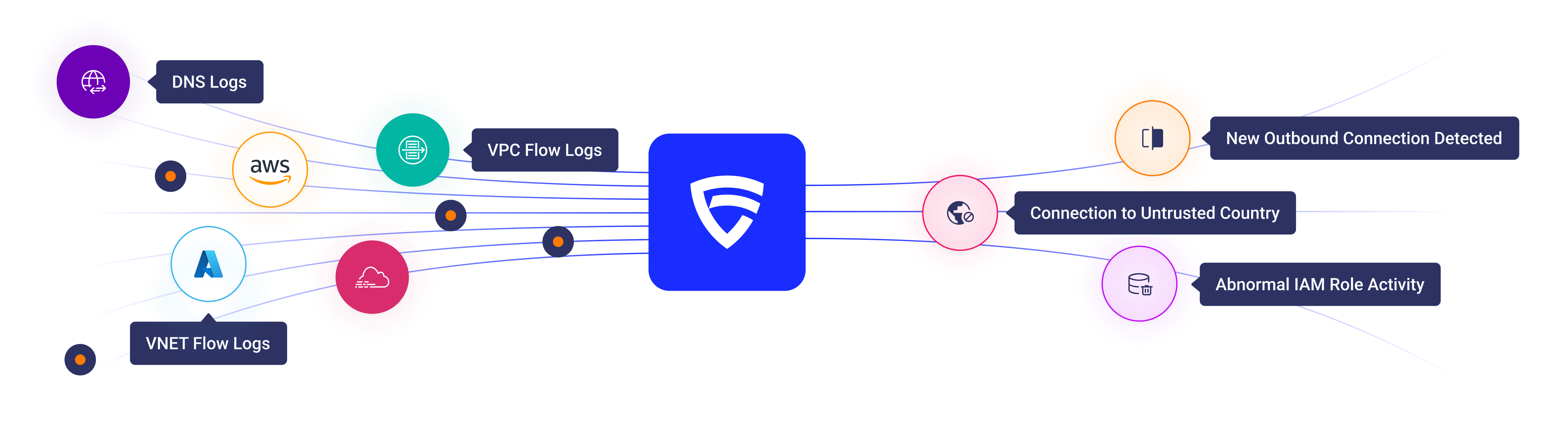
CloudFence fills the gap left by traditional network security tools that fail to scale in cloud environments. By moving beyond static rules and appliances, we deliver agentless, behavior-driven visibility, from cloud native logs, to detect deviations very early, stopping threats and lateral movement before they escalate.

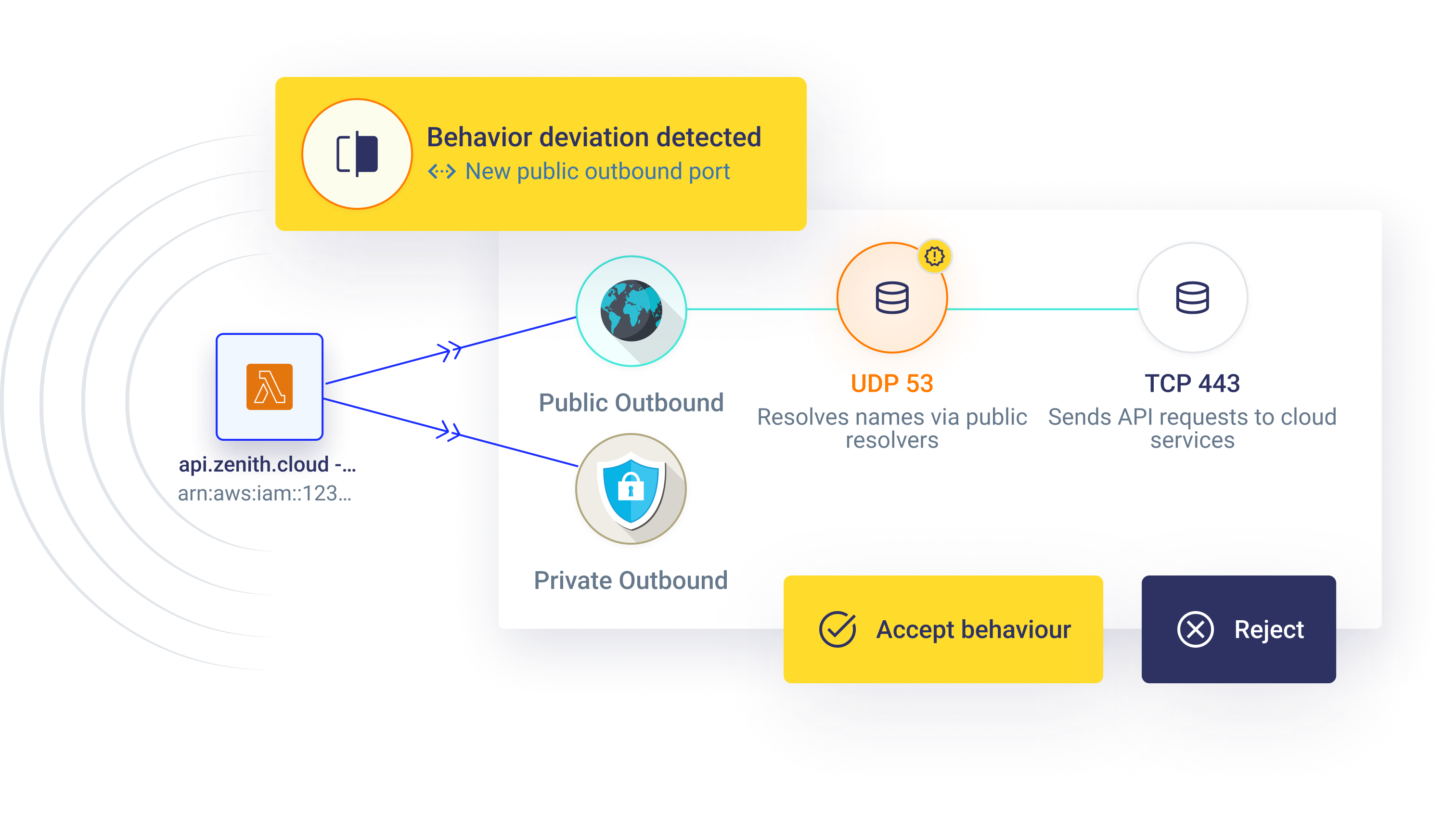
Runtime Behavioral Baselines
Stop Running Your Cloud Without Behavioral Visibility
CloudFence builds per-workload behavioral baselines from native cloud logs - enabling real-time detection of deviations such as new ports, unexpected east-west communication, abnormal outbound activity, and unusual identity operations.

Usage-Based Least Privilege
Enforce Least Privilege from Observed Behavior
CloudFence continuously evaluates runtime traffic flows and identity activity against security group configurations and IAM permissions - surfacing unused rules, overly permissive access, and excessive role privileges to drive precise, usage-based least-privilege enforcement.


Egress Traffic control
See Where Your Data is Going and Detect Risky Egress Traffic
CloudFence continuously analyzes outbound activity across accounts and VPCs, classifying domains by reputation and category, detecting newly observed and rarely contacted destinations, and alerting on communications with high-risk domains or untrusted geographies to mitigate data exfiltration and command-and-control threats.
Powered entirely from your native cloud logs - no agents or traffic mirroring required.


Cloud Network Map
See How Your Cloud Workloads Communicate
CloudFence provides a real-time visual map of workload communications across regions, accounts and VPCs, helping teams understand cross-VPC and cross-region connectivity at a glance. Click into any asset to view its inbound and outbound traffic, and see who it communicates with across your cloud environment.


The Behavioral Security Layer Your Cloud Is Missing
Move beyond static rules and legacy network appliances in the cloud. Detect behavioral deviations, enforce usage-based least privilege, control egress traffic, and visualize workload communications - all powered natively from your cloud logs


